Summary
SOC 2 compliance defines how organizations manage, protect, and control customer data across systems and processes. At its core, SOC 2 requirements establish a standardized framework for evaluating security, availability, processing integrity, confidentiality, and privacy controls. SOC 2 compliance is important because it provides independent assurance that a business handles sensitive data responsibly, reducing risk for customers, partners, and regulators.
What Are SOC 2 Requirements?
SOC 2 requirements are a set of compliance standards developed by the American Institute of Certified Public Accountants (AICPA) to evaluate how service organizations manage customer data. These requirements apply primarily to technology companies, SaaS providers, cloud platforms, data processors, and any business handling sensitive or regulated information.
Unlike checklist-based compliance frameworks, SOC 2 is principles-driven. It focuses on whether an organization has designed and implemented effective internal controls aligned with defined trust criteria rather than enforcing a one-size-fits-all rulebook.
A completed SOC 2 Report provides independent validation that these controls exist and operate as intended.
Why SOC 2 Compliance Exists
SOC 2 compliance exists to solve a fundamental trust problem in modern digital business: customers cannot directly observe how a company protects their data. As organizations increasingly rely on third-party vendors, cloud providers, and software platforms, assurance must come from an independent audit process.
SOC 2 compliance requirements help:
- Reduce data security and privacy risks
- Establish trust between service providers and customers
- Support enterprise procurement and vendor risk programs
- Demonstrate operational maturity and internal governance
- Align security practices with regulatory and contractual expectations
SOC 2 does not replace laws or regulations. Instead, it provides evidence that controls supporting those obligations are in place and functioning.
How SOC 2 Compliance Works
SOC 2 compliance is assessed through an independent audit conducted by a licensed CPA firm. The auditor evaluates whether management’s controls meet the defined criteria and whether those controls operate effectively over a specific period.
SOC 2 audits are based on the Trust Services Criteria (TSC), which include:
- Security (mandatory for all SOC 2 reports)
- Availability
- Processing Integrity
- Confidentiality
- Privacy
Organizations select which criteria apply based on their services, data flows, and customer obligations.
The SOC 2 Trust Services Criteria Explained
Security (Required)
The Security criterion evaluates whether systems are protected against unauthorized access, disclosure, or damage. This includes both logical and physical safeguards.
Controls typically cover access management, network security, vulnerability management, incident response, and risk assessment processes. Every SOC 2 report includes Security, making it the foundation of SOC 2 compliance requirements.
Availability
Availability focuses on whether systems are operational and accessible as committed or agreed. This criterion is especially relevant for SaaS providers, hosting platforms, and infrastructure services.
Auditors review capacity planning, system monitoring, disaster recovery, and business continuity controls to determine whether availability commitments are supported.
Processing Integrity
Processing Integrity evaluates whether system processing is complete, valid, accurate, timely, and authorized. This criterion matters most when systems perform critical business functions such as financial transactions, data transformations, or automated decision-making.
Controls often include input validation, error handling, change management, and quality assurance mechanisms.
Confidentiality
How private information is shielded from unwanted disclosure is the subject of confidentiality. This includes customer data, intellectual property, and proprietary business information.
Encryption, data classification, secure disposal, and access restrictions are common control areas under this criterion.
Privacy
Privacy focuses on personal information and how it is collected, used, retained, disclosed, and disposed of in accordance with privacy commitments and applicable regulations.
Controls typically align with privacy notices, consent management, data subject rights, and breach response procedures.
SOC 2 Type I vs Type II Reports
SOC 2 reports come in two formats, each serving a different purpose.
SOC 2 Type I
A Type I report evaluates whether controls are designed appropriately at a specific point in time. It responds to the question, “Are the controls in place?”
Type I reports are often used by early-stage companies or organizations seeking initial validation.
SOC 2 Type II
A Type II report evaluates both design and operating effectiveness over a defined period, typically 6–12 months. It answers the question: Do the controls work consistently over time?
Most enterprise customers and procurement teams require a SOC 2 Type II report.
Step-by-Step SOC 2 Compliance Process
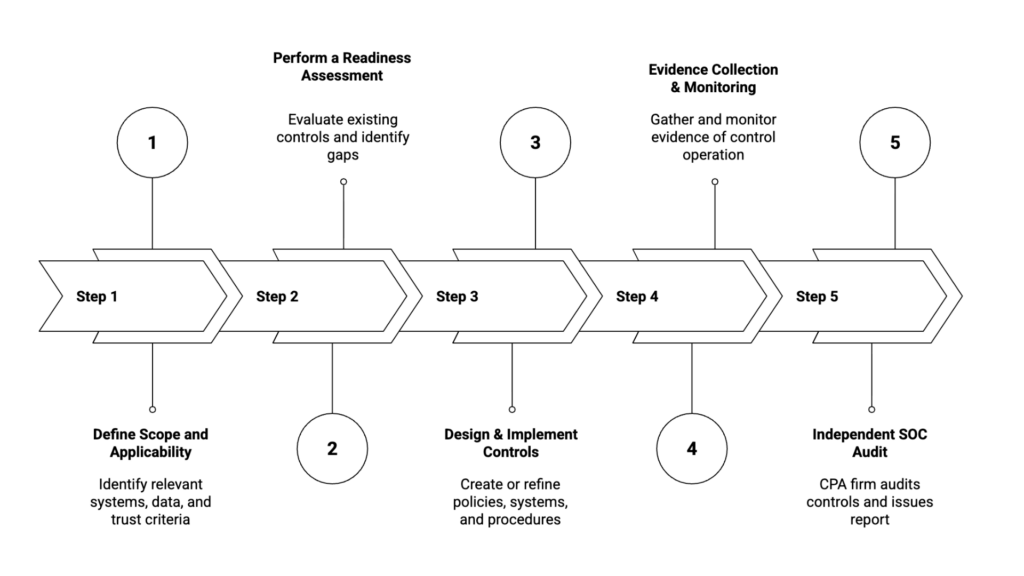
Step 1: Define Scope and Applicability
The process begins by identifying systems, services, data types, and trust criteria relevant to the business. Over-scoping increases audit complexity; under-scoping creates customer risk.
Clear scoping ensures the SOC 2 report aligns with real operational risk rather than theoretical compliance.
Step 2: Perform a Readiness Assessment
A readiness assessment evaluates existing controls against SOC 2 compliance requirements. Gaps are identified across policies, technical safeguards, and operational procedures.
This phase often uncovers undocumented practices or informal controls that need formalization.
Step 3: Design and Implement Controls
Organizations then design or refine controls to address identified gaps. This includes writing policies, configuring systems, training staff, and establishing evidence-collection processes.
Controls must be practical, repeatable, and auditable.
Step 4: Evidence Collection and Monitoring
During the audit period, the organization collects evidence demonstrating that controls operate as intended. This may include access logs, incident records, approvals, and system configurations.
Consistent monitoring is critical for SOC 2 Type II audits.
Step 5: Independent SOC Audit
A licensed CPA firm conducts the SOC audit, testing controls and reviewing evidence. Findings are discussed, remediation may be required, and the final SOC 2 report is issued.
SOC Audit Requirements Businesses Must Understand
SOC audit requirements extend beyond technology. Auditors evaluate governance, risk management, human processes, and documentation.
Common audit focus areas include:
- Logical and physical access controls
- Change management and system development
- Incident detection and response
- Vendor and third-party risk management
- Employee onboarding and termination
- Data retention and disposal
SOC 2 compliance is not a security tool—it is an assurance framework built on evidence and consistency.
Benefits of SOC 2 Compliance for Businesses
SOC 2 compliance offers tangible operational and commercial advantages when implemented correctly.
For startups, SOC 2 helps establish early trust with enterprise buyers and accelerates sales cycles. For mid-market and enterprise organizations, it reduces vendor risk friction and supports regulatory alignment.
Additional benefits include improved internal controls, clearer accountability, reduced security incidents, and stronger governance structures.
SOC 2 compliance is often viewed externally as a security signal, but internally it functions as an operational discipline.
Industry-Specific Use Cases
SaaS and Cloud Providers
SOC 2 helps SaaS and cloud companies pass enterprise security reviews by clearly documenting how customer data is protected, who can access it, and how incidents are detected and handled—reducing deal delays during procurement.
Financial Technology Companies
For FinTech organizations, SOC 2 demonstrates how financial data, transactions, and system availability are protected through access controls, monitoring, and change management—building trust with banks, partners, and investors.
Healthcare and Data-Driven Businesses
SOC 2 validates the technical and administrative controls used to safeguard PHI and sensitive data, supporting HIPAA compliance, vendor risk assessments, and secure remote access across cloud-based healthcare systems.
Common SOC 2 Compliance Challenges and Mistakes
- One common mistake is treating SOC 2 as a documentation exercise rather than an operational one. Controls that exist only on paper rarely survive audit scrutiny.
- Another challenge is inconsistent evidence collection. Controls must operate continuously, not only during audit windows.
- Over-engineering controls can also backfire. Complex processes are harder to follow, harder to audit, and more likely to fail.
- Finally, misunderstanding scope leads to reports that fail customer expectations, even if technically compliant.
Cost, Time, and Effort Expectations
SOC 2 compliance costs vary based on organization size, scope, and maturity, and readiness timelines are driven by how effectively existing controls operate in practice. Readiness efforts may take several weeks to months when gaps exist in access, monitoring, or documentation.
Type I audits are typically faster and less resource-intensive than Type II audits because they evaluate control design at a specific point in time. Type II compliance requires sustained operational discipline and continuous execution over an extended period.
Indirect costs—such as internal staff time, tooling, and process changes—often exceed audit fees and should be accounted for early in planning.
SOC 2 vs ISO 27001: Decision Support
SOC 2 and ISO 27001 are often compared but are designed to solve different business needs.
SOC 2 is a U.S centric assurance report focused on service organizations and building customer trust, while ISO 27001 is a certifiable international standard centered on establishing an information security management system.
SOC 2 is typically preferred for customer assurance in North American SaaS markets, whereas ISO 27001 supports broader global regulatory and compliance alignment.
Many mature organizations pursue SOC 2 first to satisfy customer demands, then adopt ISO 27001 over time to standardize security governance.
Future Trends and Best Practices in SOC 2 Compliance
SOC 2 compliance is evolving toward continuous assurance models supported by automation and real-time monitoring. Customers increasingly expect updated reports, not annual snapshots.
AI-driven security monitoring, integrated compliance platforms, and tighter vendor risk expectations are shaping future audits.
Best practices emphasize control simplicity, automation, and alignment with actual business risk rather than compliance theater.
Organizations that embed SOC 2 requirements into daily operations experience lower audit friction and stronger long-term resilience.
Organizations working with ChampSoft often streamline SOC 2 compliance by aligning audit scope with real operational risk.
FAQs
What are SOC 2 requirements?
SOC 2 requirements are control standards based on Trust Services Criteria that evaluate how organizations protect and manage customer data.
Is SOC 2 compliance mandatory?
SOC 2 compliance is not legally mandatory, but it is often required by customers, partners, and enterprise procurement teams.
How long does SOC 2 compliance take?
Initial SOC 2 readiness and audit processes typically take several months, depending on control maturity and scope.
What is included in a SOC 2 report?
A SOC 2 report includes the auditor’s opinion, system description, control objectives, and test results.
Who needs SOC 2 compliance?
Technology companies, SaaS providers, and service organizations handling sensitive customer data commonly require SOC 2 compliance.